Can You Repair Your Past? | Reputation Management 2021
Can you repair your past with reputation management? This article explains the exact steps necessary to clean up your background with a reputation management team. We all make mistakes in our lives, and, sometimes, people will use those mistakes against you. You can’t undo past behaviors but you can make sure that you no longer become the object of gossip. In this article, we present a number of strategic actions that you could take to achieve this.
There are five major steps to repairing your past to manage your reputation. One of the first questions to ask yourself is whether your past needs repairing. The truth is each of us may need some form of reputation management during the course of our lives.

How to Repair Your Past with Reputation Management
1. Ignore What People Say
First, you have to stop listening. If you regularly remind yourself of the bad things you did, it is bound to affect you. Hence, learn how to stop taking it personally.
“A person is not affected emotionally by what happens around them, but by their interpretation of what happened. In turn, our interpretations are formed by our beliefs.”
2. Decide On Your Desired Image
Next, you have to decide how you want people to view you instead. Forget about the things that happened in the past and think about the future. It takes a long time to build a reputation, but it would take even longer if you don’t know what you want that reputation to be!
“Know what your brand stands for, and know what your brand promises. Your brand promise should be precise and attainable, and you should be able to communicate it clearly.”
3. Bring in the Professionals
You may also want to work with a professional reputation management company to help improve your reputation. We know how to develop strategies and action that improve your reputation. We also know how to remove negative comments or suppress your past so that it will no longer haunt you. Mainly, we are on your side and we understand what you are going through. A professional reputation management service such as ours offers a number of important benefits.
4. Be Honest
When people attack your reputation, you can turn things around by owning the narrative and controlling it. Repairing your past becomes second nature. Those who attack you hope that they can point out your flaws. If, however, you immediately accept that you have made mistakes, and point out how you have improved since then, you take the power away from them.
5. Make the Necessary Changes
If you truly are honest about the mistakes that you have made, then you should also be able to see how and where you can improve. Hence, you must put actions in place to make those improvements. For instance, if you delivered poor customer service, you could invest in your employees to improve this. If you have a reputation for overcharging, you could offer a price guarantee. People are very forgiving, particularly if you demonstrate that you have learned from your mistakes.
As long as you have an open mind, you can learn from every experience you have, whether it’s good or bad.
What’s Next?
Repairing your past with reputation management is a complex thing. On the one hand, reputation is your most valuable asset. On the other hand, it is also something you have no control over. No matter how hard you try to do things right, there will always be skeletons in your closet waiting to come out, there are always mistakes to be made, and there are always people just waiting for things to go wrong.
Therefore, the best you can do is to give them as little opportunity for that as possible and, mainly, to consider every experience as a learning experience and turn it into a positive.
Within the next three business days or 72 hours, a reputable removal service can have your negative information removed or dramatically suppressed. If you’re ready to repair your past or have additional questions, contact us today.
How Are Employers Viewing Background Checks?
Employers are viewing your background. You may be wondering whether your prospective employers are looking into your background. The simple answer to that is: “yes, they are”. They do this for a variety of different reasons. You may need government security clearance or have significant financial responsibilities. In addition, you may be working with vulnerable people and employers want to know if they can trust you.
Either way, more and more, background checks are becoming a standard procedure during the hiring process and it is vital that you are aware of this. A recent survey by Endora reveals the extent to which background checks are conducted – and why, sometimes, they aren’t.
While more than 98% of businesses conduct pre-hire background checks on potential new employees, less than one-quarter of businesses proactively screen current employees – exposing CEOs and Boards to significant safety, security and compliance risks.

Is it Legal for Employers to View My Background?
Thus, if you are curious whether there are employers viewing your background, there is nothing wrong with prospective employers conducting a full background check. You will usually have to give permission, which means you will be aware of these checks. Furthermore, the federal Fair Credit Reporting Act (FCRA) is there to protect your rights as well.
The federal Fair Credit Reporting Act (FCRA) promotes the accuracy, fairness, and privacy of the information of consumer reporting agencies. There are many types of consumer reporting agencies, including credit bureaus and specialty agencies, i.e., about check writing histories, medical records, and rental history records.
Employers viewing your background take into consideration the FCRA regulations, which also stipulates how old the information contained on these reports can be. This means that you should know yourself exactly what a prospective employer will find out about you. Should any of that information be less than positive, you may consider disclosing this before the search is complete.
That said, prospective employers also perform other types of background checks. One of these is to ask you for past references. These will usually be employment references, unless you are fresh out of school or college, in which case they can be academic or even personal references. These references are designed to get to know you as a person and worker.
What About Internal Privacy Policies?
Keep in mind that, even if an employer asks for the background information listed above, and it is legal, the former employer does not have to answer. Many companies limit what they will disclose about former employees. Sometimes this is for fear of lawsuits for defamation. Other organizations may not release information due to internal privacy policies.
The other thing that many employers will do is screen your social media profiles. This, they believe, will give them an even greater insight into who you are in your personal life.
Employers Viewing Your Background, What’s Next?
Be aware of the fact that employers will look you up before they hire you. Clean up your social media profiles, get copies of your credit report, arrest records, and “Google” your name for more information, etc. Therefore, to make it difficult for employers to view your background online remove any negative items you find about you.
- Remove them yourself. Ask the website owner (s) to delete the damaging information about you.
- Contact a removal team who works with a legal team to remove your negative data
Either of the above two methods will eliminate any doubt about what others will find when searching your name in Google. In fact, you should ask for a copy of your personal Lexis/Nexis Accurint Person Report, which is a free report. This report prepares you for what a prospective employer will see about you. If you don’t like what you see, then contact a reputation management firm, like Guaranteed Removal, to help you improve it.
Employers are viewing your background, unfortunately, if you have questions about how to clear your background quickly and safely, contact our professionals.
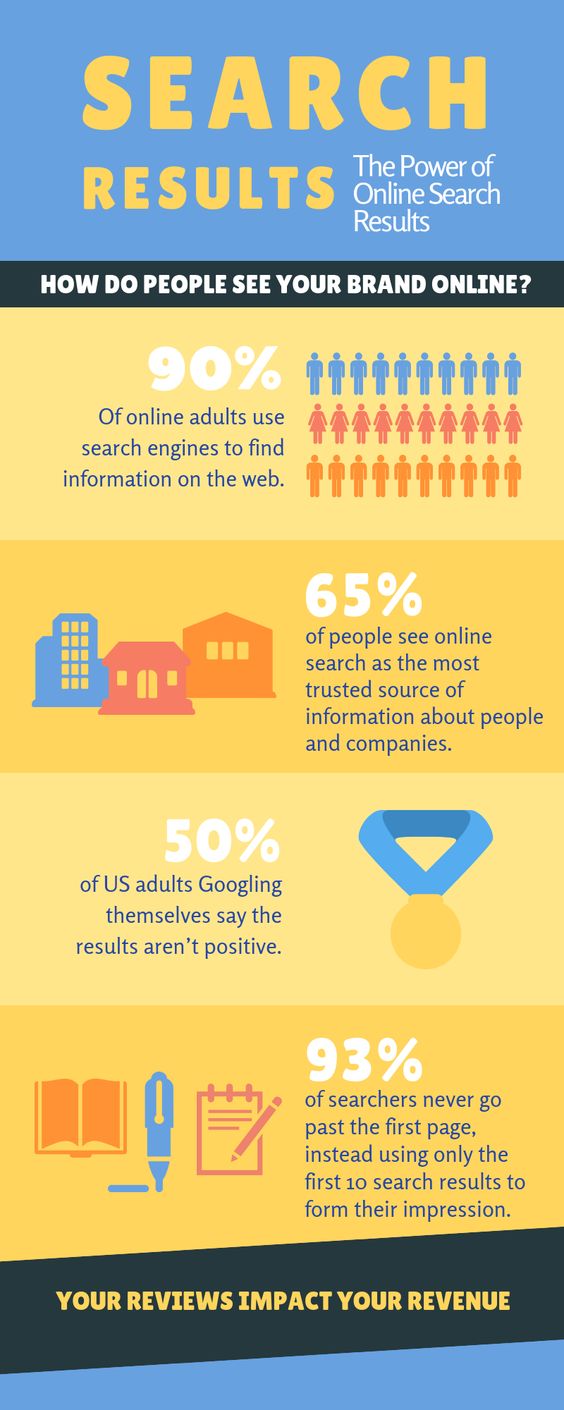
How Are You Viewed Online? 2021 Solutions
Viewed Online | Most of us spend a lot of time online looking at other people’s social media accounts. Recent research has shown just how much of an impact this has on people. For instance, it stands to reason that those who post a lot of negative things online as negative people.
Yet, those who post a lot of positive things can come across negatively as well. Those who talk quite openly online about how happy they are with their relationship tend to be happier in themselves but liked less by others. What you share online is also very important. People who talk about themselves and their achievements can often come across as bragging.
One thing that few people consider, however, are the responses they receive online and how that clouds other people’s judgment. Psychologically speaking, we find second-hand information about an individual more reliable because individuals will usually talk about themselves in a more positive, but perhaps not entirely honest, manner. You can not believe everything viewed Online

The Impact of Positive Posts on Facebook
A recent piece of research has been completed that looked at the impact of positive posts on Facebook in particular. Four positive status updates were created on four different profiles and they belonged to four categories, as shown below, and their responses were very interesting:
Personal self-authored, meaning that the profile owner wrote the post and talked about himself or herself in a positive light. Readers saw this individual as more competent and physically attractive. They also saw these individuals as very confident.
General self-authored, meaning that the profile owner wrote the post and talked about an activity or opinion, rather than his or her own achievements. Readers saw this as even more competitive as well as being more appealing as a friend.
Personal friend-authored, which means someone else wrote about the profile owner in a positive light. Readers saw these individuals as more appealing as a friend. They also saw the profile owner as more popular and modest, but not as confident.
General friend-authored, meaning someone else wrote the post and didn’t talk about the profile owner. Readers saw these individuals as modest.
What Does This Mean?
It essentially means that someone who shares a lot of information about themselves may be bragging. Someone who is talked about by others in a positive light is someone who is more likable and popular.
That said, this study looked specifically at the impact of social media. If you look yourself up online, plenty of other things may appear as well. Past and current work history listed, as well as criminal convictions. There has been a surge of the latter in recent history because criminal records are now being digitized and there are third-party organizations that have made these publicly available.
You may also have been featured in a newspaper or other sources of media, and those documents are publicly available. All of that has an impact on how people see you when they look you up online.
Finding a Balance
Everything seems to be about finding a balance. If you appear in many different professional publications, you may come across as an expert in a certain field, but this could be intimidating to those with lower standards of education. Similarly, if you have featured in an opinion piece, you could attract those who share your opinion and alienate those who don’t. A criminal record, viewed online unsurprisingly, is never a positive thing and will not portray you in a good light.
Social media (read more) is complex because it is very different to look at yourself through the eyes of someone else. It is important to consider, therefore, what you post and in what tone you post it. Perhaps there is something about sticking to cat videos when it comes to sharing information on social media, although it is likely that there are some people who would find you incredibly boring for doing so. Learn how to remove negative articles on the internet with the help of our experts.
Oops! We could not locate your form.
How to Remove Images From Google
How to Remove Images From Google
When was the last time you Googled yourself? What do you think you’ll find? Odds are, not much. Especially if you tend to keep an “under the radar” type of lifestyle.
Whether you like it or not, your personal data and images can be found online within a few simple clicks on Google. You may not surf the web or be as tech-savvy as your 10-year old nephew, however, people are looking you up.
In 2018 alone there were more than 2.9 million cases of identity theft. That’s is only what was documented. Hackers and cyber-criminals that exist on the dark web have the capability to ruin your reputation.
That is why it is imperative to know what information is online about you and what you can do to improve your reputation. Build your safety net online with GuaranteedRemoval.com.
Oops! We could not locate your form.
Types of Images Google WILL Remove
We get a lot of phone calls on a daily basis asking why Google won’t remove a photo that they deem negative or “unwanted”.
In order to give our clients a better understanding of how Google search results works are by thinking of Google like a librarian. Think of it this way – you tell Google your question and they point you in the direction of the best possible answer, the search results.
The same goes for a librarian, you ask them for a book and they point you in the right direction. The problem here is that the librarian does not own the books, nor does Google own these websites.
Due to internet privacy and censorship statutes, Google cannot pick and choose what shows within the SERPs and in what order.
For this reason, the only way Google will remove images from their search results is if it breaks their guidelines.
Here is a shortlist of possible images that could be removed due to a breach in Google’s policy:
- Trademark & Copyright Infringement
- Slander/Defamatory Posts (*must have proof)
- Elicit Photos of Minors
- Mugshots of minors, law enforcement, and other high ranking public officials
Types of Images Google WILL NOT Remove
From the previous section, you can get an idea of what we are about to say…
Google will NOT remove any images just because you don’t like seeing them online. There must be legal documents, proof to discredit the post, or a license claiming you own the content they published.
For most, this is impossible. Most websites have fine print within their disclaimers stating when you post on the platform, they own the content.
For example, let’s say you just bought a new bathing suit and wanted to post a photo on your Instagram to show your friends. You do so, but 5 minutes later your neighbor’s son Tommy finds it, screenshots it and shares it on his profile! Technically, once you post anything on Instagram you do not own it anymore. Other accounts can share it as they wish with no repercussions. You cannot legally demand Tommy to remove it. The only route you have is to befriend him or his Father and kindly ask.
Be careful about what you post online, because you really never know who is going to see it, or what they are going to go with it.

What to Do When Search Engines Won’t Remove an Image
If you come across an image or even a webpage you deem negative towards yourself you have a few options.
Third-party websites that post your information (most of the time) are doing so legally.
For this reason, you should directly contact the webmaster or editor of that webpage to request removal options. Most of the time you only get one shot at this.
First impressions, just like your online reputation can make an everlasting impression. You need to proceed with caution and an open-mind when contacting the site owner.
Utilize Google Chrome extensions such as Hunter.io to locate viable email addresses. Once you obtain these contacts send something along these lines in a message, “We think the image you posted on your website is impeding on my reputation and character, because….. and here are the supporting documents….”
Make sure to again use supporting documents and any resources you have at your disposal as you work to remove an image from Google search.
The chances of having your photos removed from Google and even the direct source is slim to none. If you are unable to discredit the post or influence them to change their mind that image may show up in Google indefinitely.
What to Do When the Image is Not Removed From the Site
So what do you do when you cannot locate contact information and Google is not helping with getting your image removed from Google search? Where do you turn to when you have exhausted all of your options.
This is when it gets tricky if you are not tech-savvy.
When it comes to suppressing unfavorable images and unwanted content online that you cannot remove, the only viable option is publishing new content. Do this in high volume and daily for at least the few several weeks.
Sites such as Vimeo, Crunchbase, and Slideshare are great candidates for uploading new content that will stick. Unlike others who tell you to simply post to Facebook, you need to diversify your efforts.
Oops! We could not locate your form.
Burying Personal Information on Google Search Results
If you cannot remove images from Google will the assistance of the site owner of Google directly, what can you do?
This method is simple in theory however takes an immense amount of work to bring your desired results to life. Thanks to Facebook, Instagram, and various other social media platforms sharing new content online has never been easier.
Not seeing any photos of yourself? Make a Pinterest and add 5 new photos each week for a month and see what happens. The odds are some of those images may begin to rank of Google, Bing, and Yahoo.

Working to remove an outdated content page, on the other hand, is quite simple. Let’s say within the search results for your name there is some negative connotation however when you click on the link the webpage is dead. In other words, it would prompt an ERROR 404 code.
This can be fixed with a quick visit over to Google Search Console’s Link Removal Tool. Here you simply copy and paste the dead URL and submit for Google’s approval. Within a few days, Google will work to recrawl and remove it from their search results.
What Type of New Images Should You Post to Outrank the Negative?
When it comes to publishing new content online the main key is to post different photos. Do not post 15 selfies and expect Google to flood the search results with camera shots 5 inches from your face.
Instead, gather photos from overtime in different scenarios that showcase various actions or things being done. For example, post vacation photos, photos with friends, photos of just yourself, sports events, concerts, and much more.

The point here to make sure Google does not view each individual photos similar in any way other than your face being consistent across them all.
As we previously stated, make sure you diversify your online portfolio when it comes to social media. Do not post all your photos at one time onto Facebook and store them in a singular album…
Instead, post one photo to Facebook, one on Pinterest, one of Twitter, maybe even one of SlideShare. But you get the point, do not put all of your eggs in one basket. Don’t forget to include your name in your handle, bio, any description, and alt tags when you can. These are easy signals for Google to read and confirm this page is surely about you.
High-quality & Engaging Images
Look about your search patterns on social media. Do you tend to quickly scroll past distort/pixelated photos OR you find yourself immersed in these thrilling HD photos where you can see every detail? Yeah, we thought you’d choose the latter, smart choice.
Nobody wants to take the time to view a poor quality post. As someone people refer to these types of posts as “cringe”. With the ability to quickly tank your follow count and make suppressing anything online even that much harder.

Use Alt Tags, Title and Add Your Name Wherever You Can
We briefly touched upon this topic a few sections prior. When it comes to Google, there are many factors they consider before ranking a specific photo anywhere.
A few quick tell-tale signs that an image is about a specific person is by adding that individual’s name into various fields. But also being cautious not to keyword stuff, this is penalized by Google. That essentially means you copy and paste your name over and over again, where in the past that would work.
Nowadays, Google is much smarter than we give credit. Using broad search and semantics, Google’s algorithms to able to identify and point users in the right direction even if they misspell something, use a synonym, or are slightly off-topic.
GuaranteedRemoval: 100% Guaranteed Image Reputation Solutions
By now you should understand how anything negative or unflattering about your came to appear online in the first. However, you also have come to learn there are a plethora of methods you can implement in order to slow down any negative impacts it may have on your life long-term.
By utilizing social media and publishing consistent, high-quality content you have the capability to suppress and flood out any negative search results (photos or webpages) with perseverance and persistence.

If you have tried to accomplish this feat on your own but have seen little to no success. Please complete the contact form below and one of our knowledgable reputation analysts will contact you within 24-hours to discuss any questions or concerns you may have.
Remember the internet as a double-edged sword… Do you know what Google says about you?
Oops! We could not locate your form.
10 Cyber Security Myths Everyone Should Know
Learn about the top ten cyber security myths and what you can do to protect yourself online today.
Back in the 1990s, the internet was frequently described as “a domain for those nerds”. But sadly, that reference has been reiterated by a US White House official describing how cybersecurity is perceived now. There are over 3 million cyber-attacks that occur online on any given day.
We’re setting a precedent for a stressful occasion by decreasing safety to all those”nerds”. Everyone who operates online or frequently “Googles” to get answers to all their questions. It is important to understand the internet and how cybersecurity threats come into play.
With many cybersecurity myths hovering above, the haze about a sensible evaluation of the present situation is not likely to be eliminated quickly. Because of this, it’s quintessential for all of us to debunk such truths until we talk about the true dangers of working on the internet in 2019.
Oops! We could not locate your form.
Myth #1: It’s Just a “Threat”
The cyber security myth Classifying business risk as only”cyber threat” will just undermine the gravity of this threat. In a much-viewed part in Forbes magazine, a reporter educates readers about how cyber threat encompasses intellectual property and the security of employees. More importantly how it requires equal attention from senior executives and management staff.
Saying, “Oh, this would never happen to me”, which we will get into shortly is simply an ignorant statement. The internet is home to billions of users, one would only be being naive if they thought nobody would ever come after them. This happens to everyone.
People today treat cyber protection and preventive measures like a fire drill back in grade school. Everyone knows the motions and what they should be doing, however, they never anticipate employing what they learned. Unlike a fire, your reputation is something that must be managed proactively. Your reputation symbolizes somewhat of a safety net per se, it is there to catch you and protect your public image if something unfortunate (such as a negative life event i.e. an arrest) were to occur.
Myth #2: Will Never Happen To Me
It can be natural to lean toward thinking cybersecurity is a challenge unlike what you have ever faced before. But history will say nothing is genuinely new. Back in the Victorian age, when communications and trade underwent a shift with innovations in engineering, the danger perceived was not any different.
The notion that you are somehow protected by an invisible shield where your personal information will never be at risk is a statement far from the truth. However, most individuals don’t believe they are ignoring any problems. When it comes to topics such as your online reputation you cannot wait until something happens before you decide to take action.

As we opened up this article we mentioned a statistic. There are over 3 million cyber attackers EVERY DAY. That amounts to over 1 billion internet security breaches each and every year. To put this more into perspective, the world population is 7.53 billion, 35% of which own smartphones with an internet connection. This breaks down to roughly 2.6 billion individuals that have the ability to expose or potentially leak your personal information across the globe in a matter of seconds.
Let that sink in before we move on…
Myth #3: An IT Problem
Knocking down cybersecurity into an”IT problem”. Cyber risks once designated as “IT hazards” will just promote issues throughout the whole business.
It is vital to understand, cyber dangers cut across sections and that is what’s menacing. Information once digitized, there is no earmarking cyber hazard to some department.
Once a third party gains access to your system(s) it can spread like wildfire.
Myth #4: Cyberattacks Are Not Common
Cyber attacks are typical –many organizations are assaulted every day. Counting the number of cyberattacks is a useless exercise since it’s as excellent as counting bacteria or grains or rice. Although the government does their fair share or reporting these acts, just like any crime we can never fully grasp to the entry of what’s going on.
Wise action is to assess the risks and reevaluate the best way to manage them. Since this can happen to anyone there should be options for everyone. Not just those individuals with deep pockets and media connections. That is where Guaranteed Removal steps in, for the past decade we have assisted thousands of satisfied clients at removing negative content online, promoting themselves in a positive light as well as constant reputation monitoring to ensure they are out of harm’s way for many years to come.
If you are interested to learn more about how our specialists can help you take back control of your online reputation please complete the form below. We will conduct a comprehensive analysis where our team will scour the internet in search of any negative or unwanted information online. What do you have to lose? It’s free!
Oops! We could not locate your form.
Myth #5: Basic Software Will Suffice
Focusing on applications isn’t secure enough. Although good applications are essential to shield cyberattacks. It’s not sufficient to see the software in isolation. Other people are the numero uno hazard. It’s vital that you invest in training your own tools and enhance the efficacy of cyber applications, thus, striking a nice balance between security and usability.
When most individuals purchase a laptop or computer from a place such as Best Buy they tend to decline the added security measures. Most simply look at this as “oh great, another cost. Do I actually need this?”. And the answer is yes, 100% yes. You are spending your hard-earned money, from a few hundred in upwards of thousands of dollars to a piece of technology you are going to be spending a great deal of time on.
Myth #6: Cyber Criminal Don’t Target SMEs
Hackers can quickly get your data, which might be valuable. A report printed in 2015 from HM Government affirms the susceptibility with 74 percent of SMEs reporting a security violation.
Anyone that owns a business is vulnerable to cyber-attacks and data leaks. Whether it is your client list, inventory reports or marketing plans. If a hacker breaks into your database, your future plans for your business could be ruined overnight.
Nobody is excluded from cybercrimes. The key is to limit your exposure and chances that it will happen to you. Being a business, this places you at a greater risk. Individuals that go after SMEs and wealthy individuals are in it for the money. Most of the time it doesn’t matter how much they take. Hackers do this both for a living (to make an income) as well as for fun just to see “if they can do it”.
Myth #7: Manufacturers Provide Safe Systems
Producers are liable for a safe system. True. Device makers need to be more accountable for producing secure products that are robust. However, it’s often people that are unpredictable and undependable. People today find ways to bypass security by utilizing devices which aren’t so secured–tablets and smartphones.
Myth #8: Nobody Wants My Information
Maintaining and sharing info online is obviously likely to be an issue, lest we cope with it earlier. End-to-end encryption via a VPN is a secure means of sharing data over the net.
Watch this short video about what you can do today to take extra care that your reputation and online presence is in good standings.
Myth #9: The Internet Restricts Certain Actions
You’ll have remote access to your house devices. But by design, it makes your house more vulnerable than ever. It’s estimated that producers will soon recognize apparatus are possible avenues to our sensitive data and behave accordingly.
As we begin to see more and more “smart devices” it has become a larger concern about their security measures. For example, Amazon offers a doorbell to the market that has a camera or maybe a pin pad to enter a 4-digit code to enter the home. Seeing as this is a smart device and is capable of connecting to Bluetooth your home residence could be at risk.
Companies such as Target even fall victim to data leaks and financial records or customers being leaked across the dark web. No company is either too big or too small to avoid this problem. It is an epidemic and will continue to be one for the foreseeable future, unfortunately.
Myth #10: Hackers Are The Greatest Threat
Sometimes the great threat to our own reputation aren’t common cyber security myths, but ourselves.
Growing up in this digital era the times certainly changed. Children are online, browsing uncountable amounts of websites on a daily basis. As you watch them from across the room or in the rear-view mirror of your car you are unaware of what they are looking, who they are talking to, or what kind of personal information are they relaying to sites they’re visiting.
Although hackers are a great ideal in the world today, it is important that you do everything you can to ensure your reputation is protected. Keep your personal information out of harm’s way today and get started below. Again, what do you have to lose? We have your back.
Oops! We could not locate your form.
Delete Yourself from the Internet
Best Ways to Delete Yourself from the Internet
If you’re seeing this, it’s extremely possible your private data is accessible to the public. And by “public” I mean everyone on Earth!
How can you delete yourself from the internet and stop other individuals, data collection sites, or data brokers from obtaining your personal info, address, or social media accounts? Short answer: it can’t. But with some help, we can limit the risk that your personal info ends up in Google search results or data brokers’ search engines.
Regrettably, you can never remove yourself entirely from the internet, however, there are methods to decrease your online trace. Resulting in lower chances of your personal and private information being leaked online.
Here are some steps to do just that. However please advised, the deleting your data from the internet, may adversely influence your ability in the future to obtain a new job, get a credit loan, buy a home, or even try online dating.
Oops! We could not locate your form.
Delete Yourself from the Internet by Deleting Social Media Accounts and Profiles
Reminisce about what social media platforms that you have accounts on. Apart from the industry leaders, such as Facebook, Twitter, LinkedIn, and Instagram.
Do you still have unrestricted social media accounts on websites such as Tumblr, Google+, or even MySpace? What about your Reddit account?
Which online shopping websites have you registered with? Obvious choices to most may be compromised and leak your information. This includes massive online shopping accounts in addition to social media such as Amazon, Gap.com, Macys.com, eBay, and countless others. Anywhere you have an email account or online account leaves your information vulnerable to data breaches and your info ends up in search results and a target of data broker sites.
In order to successfully delete your social media, shopping, and other online accounts, you must go into your account settings. Most of the social media platforms on the market today but options within the settings called “Account”, “Manage Account”, “Privacy” or simply a button all the way near the bottom that says “Delete/Deactive Account”. That last option should be near where you can log out of the app.
If you’re experiencing difficulty with a specific social site, try exploring Google for the phrase “How to delete my account on…” followed by the name of the website you want to delete yourself from.
If for any purpose you can’t remove your social profile, modify the data within the online sites’ account (the bio or about me portion) with fictitious personal details and email accounts. Something false or entirely unpredictable that does not connect back to you in any way.
Remember to clear your cache to remove your search history and browser history when you check to see if you have completely delete social media account information. Remember to consider former employer’s staff page listings, location data, social media account data cached by old accounts and data collection, and old accounts anywhere on the internet. These all make up your complete digital footprint. Old accounts are ripe for data collection. Get rid of them to increase online security and decrease your online footprint.
People Search Removal
There are marketing databases and companies that exist online that collect your information and essentially sell it to whoever has $10 and an internet connection. These online services are called people search websites, and they have names such as Spokeo, Whitepage, Radaris, InstantCheckMate, as well as lots of others.
They accumulate personal information on their web page that stems from what you do online. This can be your biographies and about me portions, your social media presence, your website, outdated search results, shopping sites, phone company, search engine results, or any sensitive information they can get their hands on.
You have a few options when it comes to removing yourself from these infamous people search websites. You can take the route of removing them individually (over 50 databases). Here you would need to locate each website and search for yourself.
Afterward, you must track down the website master (or owner) and request that your information should be removed, and why.
The only problem with that is, that the method for deleting your information from each site changes and oftentimes it requires transmitting mail or faxes along with submitting actual tangible paperwork. In short, this is not a quick process unless you have been trained to do so.
Be warned: If you attempt to remove yourself from these people search sites and you have a minimal online reputation score it can have adverse side effects. If you are not notable online you may have trouble in the future with career and life opportunities as we briefly stated above.
GuaranteedRemoval offers a one-time solution that comes with a lifetime guarantee. Our team of removal specialists will work to scour the internet and remove your personal and private information from over 45 people search background reporting agencies.
We are your second chance.
Directly Removing Website Data
The first step you can take when removing your information and personal data online would be to register to be placed on the National DNC Registry (Do Not Call List). This will automatically remove your personal telephone number for an uncountable list of businesses.
On the other hand, if you are seeking to remove an old website post or an old embarrassing image of you from back in the day, you’ll have to communicate with the website owner for those specific websites one by one.
Most of the time websites will have a contact form if they do not wish to publicly share their contact information. One could only imagine how many calls they would receive on a daily basis if they left in on their website.
Sadly, private website operators are under no obligation to remove your posts as long as the information is factual.
So, when reaching out to these websites it is imperative that you remain polite and simply assert why you need the information deleted.

Removing Personal Information
If another individual has posted delicate personal information of yours online such as your SSN or banking information, you can send a judicial inquiry to Google so the public will lose access to these details. If everything is cleared, it’s a guarantee Google will permanently delete and remove the information from search and Google’s servers.
This removal method can last for a prolonged period of time as there’s no promise that it will ever be successful. However, it is also your most reliable resort if you discover yourself in a defenseless position with nowhere to turn.
Please note: It is important to remember that you cannot simply go online and demand random information be removed. This is for when you’ve been targeted with identity theft or something drastic. Protect your activities online to avoid this using password manager services to have super hard passwords that you don’t have to remember and use a VPN service to protect and encrypt your wi-fi.
Whether you agree or disagree with another website publishing your personal information, if the context is factual there is no legal obligation for these sites to take action.
Updating Google After Information is Removed
So by now, you have located the webpage(s) you deemed negative and unwanted and sent your initial contact attempt to the webmaster. Even after (and if) they agree to remove or update your information your job is not done yet.
Once content is removed from a website search engines such as Google, Bing, and Yahoo are left in the dark and require you to notify them of the changes.
Sure, the webmaster could update their Google Search Console and notify Google on your behalf but let’s be real, they are not going to do all this work for free. So it is your job to reach out.
When something is appearing on Google’s search results but no longer on the website itself we call this ‘cached data’. I simply email to Google or submitting to their “Send Feedback” option on the bottom of each SERP is where you should beginning.
When you scroll all the way to the bottom on Google you will see “Send Feedback”, this is where users can highlight and give a description and the alterations they would like Google’s support team to take a look at. Once they see the information has been removed they will remove it from the search results entirely.
Present the specific dead URL to Google in hopes they will update the servers by deleting the cached search result. This is your end-goal. This process may take in upwards of a few days to a week before you see results.
Keep an eye on it as you can always resubmit the dead page over and over until you see it worked.
There’s no promise that Google will delete the cached information (unless your request is 100% legitimate), however, it is worth trying to remove as much of your presence as possible from the internet.

Removing Email Accounts
Depending on the sort of email account you use, the number of actions this will take will change.
You must sign in to the account and locate the choice to delete or remove the email. Most accounts such as Gmail will remain “temporarily deactivate” in case you would like to use it again in the near future.
This is for those making an impulsive decision, they may not actually want to delete their email.
An email address is required to perform the previous steps, so ensure that you perform this step last.
Wrapping Up…
Remember to be calm as you go through the process of deleting yourself from the internet. DO NOT expect to achieve this in a day.
For others, you may have to endure negativity online if it is something you disapprove of. However, if it is not breaking any laws. Somethings do remain online indefinitely.
In summation, before you stop and give up. Contact us through the form below. We will reach out to you as soon as possible to see if we can assist in your removal needs.
Oops! We could not locate your form.
How to Protect Yourself From Online Embarrassment
How to Protect Yourself From Online Embarrassment in 2019
Have you ever heard the old saying, “once something is online it is there forever”? Well, in a sense this can be true in today’s world.
With the emergence of social networks and how easily individuals can gain access to the internet, there is always a chance that your personal information can fall into the wrong hands.
Knowing how to act is important however knowing how to prevent online embarrassment will not only save you stress but money in the long run.
In this article, we will discuss how you can use online reputation management services and popular practices to minimize the risk of online embarrassment. In addition, we will cover how to properly use social media to reduce the spread of your personal information online.
Having a plan of recourse is never a bad idea. Learn how to create crisis management strategies with the best team in online reputation.
Now let’s dive into how online reputation is assisting individuals with monitoring, maintaining, and even restoring a positive web presence.
Oops! We could not locate your form.
Using Online Reputation to Protect Yourself From Online Embarrassment
What is online reputation management? For those of you who are new to reputation management, online reputation management or ORM is the art of restoring, maintaining, and monitoring the online presence or notoriety of either an individual or a business.
When you share personal information online it is important to remember how large the internet is and how many people use it on a daily basis. Even if you are a normal person with a minimal presence online that does not mean you should stop worrying about cyber threats.
There are millions of cyber threats each year such as identity theft that cripple individuals not only financially but these threats could be an everlasting effect on relationships you have both on and offline.
It is better to start from scratch than to restore a negative reputation.
As you work to build and establish a name for yourself online it is important that you focus your efforts heavily on social media, press releases self-promotions, and SEO (if you have a personal website about yourself).
The most powerful of the three would be the distribution of press releases. Head over to Google and search for local news outlets in your area. Reach out to them and see if they offer a paid service where you write the press release and they publish it on their website for a fee.
Therefore, press releases are a sure-fire way to have new content to reach the first front pages of Google, Bing, and Yahoo.
Next, share those press releases via your social media accounts to gain more exposure.
Lastly, you can copy and paste your new release onto a custom website. Optimize it in hopes of obtaining another spot on Google’s SERPs.

Being Smart on Social Media
When it comes to sharing content online. It may be your first instinct to share funny, controversial, and borderline inappropriate content with your friends and family members.
Unfortunately, these actions can have everlasting effects on your online reputation as you grow older. If you have little to no information online about your search engines such as Google will scour the internet to find anything they can.
This could be a college photo of your drinking 10 years ago. Or an inappropriate Tweet that you thought was funny at the time.
Start by customizing your account settings and making your social networking accounts are private. This will limit the chances of anything reaching Google. Which may be good or bad depending on your situation. However, you will not have to worry about embarrassing photos appearing in the Images tab for the world to see.
Make sure the connections you make on each social platform such as Facebook, Twitter, and LinkedIn are people you trust seeing the information you post.
In other words, if you constantly post photos of you and your friends partying or on vacation. It may be a good idea not to befriend any of your work colleagues.
One easy tip to monitor yourself online is by tracking your name on Google Alerts. This tool allows you to receive instant email notifications the second something about you is published online.
Lastly, this could be a comment on one of your social platforms. Or an entire story about you posted by a third party without your consent. Google Alerts allows you to take action quickly if something negative happens online.
Control the Flow of Your Personal Information Online
So to elaborate more on how you can better control the flow of your personal information online it is important to know where you appear in the first place.
Our team here at GuaranteedRemoval.com will search over 400 websites. In search of any trace of information about you on the web.
If you would like to conduct this search yourself. We recommend searching through the first 10 pages of Google, Bing, AND Yahoo when starting out.
One of the easiest ways to control the spread of your information to set your privacy settings on social media platforms. In addition to limiting what the online world can see about you. You can also remove your information from over 45 background reporting agencies.
Otherwise known as People Search websites. These data aggregate websites house lots of personal information including your contact information, social media links, criminal history, and much more.
Furthermore, our team offers a simple removal solution to clear your name on your behalf. So, if you are interested in learning more about how Guaranteed Removal can assist you. Please fill out the form below and we will reach out to within 24-hours with a detailed solution.
Oops! We could not locate your form.
Keep Your Personal Information Private
In 2018, almost everyone has access to the internet whether it is via a smartphone or on a computer at home. While uploading photos to Facebook or Instagram may be fun, you need to keep in mind that everyone in the world now has access to your photo(s). It is essential to maintain a high level of security while writing or posting online.
Let us break down the top reasons why we feel you need to keep your personal information private. Personal reputation is how you are perceived by the world as an individual. It is the first thing anyone thinks about you when they hear your name or see your photo online. We all know that one friend that posts on Instagram 10x a day and updates his/her Facebook status regularly. You begin to form opinions about individuals that you have never even met by the way they carry themselves online. While most of this is under your control, you need to be cautious of what others do with that information you are publishing.
Oops! We could not locate your form.
Top Reasons Why Should Keep Your Personal Information Private
Identity Theft
In this digital era, we are utilizing more online applications to manage our everyday lives. Ensuring your social media accounts and banking information is secure is not difficult if you follow some easy to learn steps. Identity theft is when an individual unlawfully obtains personal/private information about someone in order to impersonate them (mostly for) financial gain.
You can avoid these cyber-attacks by using different passwords on every website. This the most simple and effective way to stop identity theft. Many individuals use one or two passwords for everything. This is great for yourself and so you can remember but what happens when a hacker finds that one password, they now have access to everything!
Therefore, creating passwords that are alpha-numeric with at least 12 characters is the way to go. If you use letters, numbers, and special characters there are over 1 Trillion variations the hacker will need to attempt. Making this task nearly impossible and in turn, safeguarding your information for good. Change your passwords every couple of months.
The next step you should take to keep your personal information private would be to opt-out from any and all background reporting databases. These sites report your exact address, links to your social media accounts, and even friends and family members.
Removing yourself from these 40+ sites will make the task of finding your personal information even more difficult for any hacker. Lastly, make sure you constantly monitor all of your accounts for possible discrepancies. By monitoring your accounts, you will know instantly if something is wrong as you can resolve the issue before it gets bigger.
Future Job Opportunities
Next, sites like Facebook, Instagram, and Twitter are morphing into your “second resume”. This is where potential employers can get a good sense of your personality, an easy way to gauge if you are the right fit for their company. Unless your profile is private, refrain from posting political or religion based posts as this may hinder any job opportunities that come your way in the future. Do not walk into your next interview blind, review your social accounts prior to applying for a position to have the best chance of getting the job.

Credit Scams
This may seem fairly straightforward for many millennials, however, for the older users of the internet, this is very important. When you are online, there are some easy indicators you can see to instantly reassure you that the site you are on is secure. Most importantly find out if a site is ‘secure’. This is simply done by looking at the website address. When you type in Google.com, there is an https:// placed before the web address. This is the SSL telling you this site is secure “https://. If there is no ‘s’ that site is not secure.
As we start to drift away from cash to plastic credit/debit cards this opens new doors for cyberhackers. When setting up your cards, again make the passwords unique and change them monthly. In addition, use a PIN nobody can guess. This means to refrain from using addresses or birthday! As annoying this can seem it will benefit you in the long run by making yourself almost invincible to cyber attacks. Next time you are visiting your bank ask them about setting up secondary privacy questions, this will automatically lock someone out after too many wrong attempts.
Closing Thoughts on Keeping Personal Information Private
Nowadays it is very tempting to use every feature that social media offers, like the location for instance. Keep in mind that you are literally telling people where you are at that exact moment. These actions leave you prone to not only identity theft but other attacks like a home invasion! Your personal address does not have to be on Facebook, even if there is a field for it. Start by reviewing the privacy policies on each website and take every measure you can to safeguard your personal information. Be smart when you are online, we live in a very transparent world, therefore keeping your information private is imperative. Call us if you see something online you disagree with, we can help.
If you are seeking more information on how to remove articles from the internet check out our recent blog!
Oops! We could not locate your form.
Tips on Fraud Prevention
By definition, fraud means a wrongful or criminal deception intended in financial or personal gain. In other words, you cannot trick somebody into doing business with you under false pretense. Fraud prevention is the efforts made to combat this criminal activity to ensure your personal information is safe. Some of the most popular forms of fraud include; financial statements, asset misappropriation, larceny, healthcare/insurance, and consumer fraud. Many individuals are unaware of fraudsters even when they are right in front of them. Make sure you know your options in case you, unfortunately, become a victim. Do not make the mistake of not caring now.
Oops! We could not locate your form.
Why Does Fraud Prevention Matter?
Fraud prevention is crucial for any business. Security risks or financial crimes may leave many corporations vulnerable to such fraudulent schemes. It is important to have a plan intact that is ready to combat fraud when needed. Constantly monitoring and improving detection features makes this process a lot easier for many businesses. It is imperative that you locate and eliminate these issues from the start. Waiting until it is too late might be your business’ demise. Here are some of the best free online reputation management tools.

Tips On Fraud Prevention in 2018
Know Thy Enemy
In 2018, the digital world is booming. Having said that, this gives a large opportunity for thieves and hackers to steal your information. It is crucial to learn as much as possible about an individual before you do business with them. Start by reaching out to previous clients they have worked to get a better sense of their credibility. See if there are any news articles about the CEO. Another viable option is to take a look at the reviews for that specific business. Review sites like Yelp, TripAdvisor or the BBB are excellent resources when determining if someone is reputable or not.
Secure Payment Methods
Nowadays, with various secure payment vendors, it is nearly impossible to see fraud occur here. Merchants such as Authoize.net or Payline Data grant the ability to process payments safely knowing you are protected. Once the payment information is entered and processed, the card information is gone for good. The only three entities that see this information would be you, the customer and the merchant account. Another popular platform for this type of solution is PayPal in my opinion. However, there are several other routes you can take, another popular choice is SquareUp.com.
SquareUp caters and works for any size company, no matter if you make under $250,000 annually or more. If you operate in the field of food, health, retail, or service and repair we highly recommend you check out this option. Why? Because you can not only process cards online but you can actually swipe their credit card at the time of purchase.

Safeguard Personal Information
The best example of a business being infiltrated is the impersonation of top management, especially CEOs. Nobody wants to make the CEO wait so when employees receive an email request from “their boss” many will answer without asking a single question. Fraudsters love to prey on administrators or secretaries as they have access to most of the important information. DO NOT provide any financial credentials unless you are paying for something. In addition, be overly cautious if somebody you currently work with is asking questions about the information they should already have. Phishing is another popular tactic in an attempt to retrieve information such as passwords or account numbers.
Monitoring
It is important to constantly monitor your accounts to ensure there is no fraudulent activity going on. By reviewing monthly/quarterly statements this will show you right away if anything suspicious is going on internally. There are many types of different software you can download/purchase. LifeLock, partnered with Norton Antivirus handles anything and everything to do with data breaches. Lifelock allows users the ability to freeze accounts at a moment’s notice so you are fully protected. How you appear online, or how popular you are may determine how frequently these attacks occur.
Call GuaranteedRemoval.com today if you are struggling with combatting fraudulent activity online. We offer an extensive list of services and solutions such as content removal, monitoring and credit restoration. It is time you finally start focusing on what counts, your business. Let our professionals handle any efforts made to minimize your chance of a cyber attack. If you are not careful you could make matters worst trying to resolve any issues on your own.
Oops! We could not locate your form.